Hashicorp Boundary Enterprise Crack is a cutting-edge access management platform designed to secure and streamline access to systems and resources in modern, distributed environments. It’s not just another security tool—it’s a paradigm shift in how we think about access control.
At its core, Boundary Enterprise offers:
- Identity-based access control: Say goodbye to IP-based restrictions.
- Dynamic host catalogs: Automatically update and manage your resource inventory.
- Robust session management: Monitor and record access for enhanced security.
Boundary Enterprise builds on Hashicorp’s reputation for creating powerful, user-friendly infrastructure tools. It’s the big brother to the open-source Boundary, offering enterprise-grade features that take security and scalability to the next level.
- The Evolution of Access Management
- Core Components of Hashicorp Boundary Enterprise
- Setting Up Hashicorp Boundary Enterprise
- Integrating Boundary Enterprise with Existing Infrastructure
- Security Features of Hashicorp Boundary Enterprise
- Scalability and Performance
- User Management in Boundary Enterprise
- Automating Workflows with Boundary Enterprise
- Monitoring and Troubleshooting
- Comparing Hashicorp Boundary Enterprise to Alternatives
- Case Studies: Boundary Enterprise in Action
- Future Roadmap for Hashicorp Boundary Enterprise
- Getting Started with Boundary Enterprise: Tips and Tricks
- Conclusion: Is Hashicorp Boundary Enterprise Right for Your Organization?
The Evolution of Access Management
Remember the days when a simple firewall and a list of IP addresses were enough to keep your systems secure? Those days are long gone. The shift to cloud computing, microservices, and remote work has turned traditional access management on its head.
Consider this: In 2019, 47% of organizations reported struggling with access management in hybrid environments. Fast forward to 2024, and that number has likely skyrocketed.
Boundary Enterprise tackles these challenges head-on. It’s not just about keeping the bad guys out—it’s about giving the right people the right access at the right time, all while maintaining a clear audit trail.
Core Components of Hashicorp Boundary Enterprise
Identity-based Access Control
Gone are the days of managing long lists of IP addresses. Boundary Enterprise License Key ties access to identity, not location. This means:
- Users can access resources from anywhere, securely.
- Access policies are tied to who you are, not where you’re connecting from.
- Admins can grant and revoke access with unprecedented granularity.
See also:
Dynamic Host Catalogs
Imagine never having to manually update your resource inventory again. That’s the power of dynamic host catalogs. They:
- Automatically discover and catalog new resources.
- Keep your access policies up-to-date as your infrastructure changes.
- Reduce administrative overhead and human error.
Session Recording and Monitoring
With great power comes great responsibility—and the need for accountability. Boundary Enterprise’s session recording features:
- Capture detailed logs of user activities.
- Allow for real-time monitoring of active sessions.
- Provide invaluable data for audits and incident response.
Setting Up Hashicorp Boundary Enterprise
Getting started with Boundary Enterprise Crack is straightforward, but there are a few key steps to keep in mind:
- System Requirements:
- A Linux, macOS, or Windows server
- At least 4GB of RAM
- 20GB of free disk space
-
Network connectivity to your resources
-
Installation Process:
- Download the Boundary Enterprise package
- Run the installer with administrative privileges
-
Follow the guided setup process
-
Initial Configuration Steps:
- Set up your initial admin account
- Configure your authentication methods
- Define your first project and target hosts
Pro tip: Start small with a pilot project before rolling out Boundary Enterprise across your entire organization.
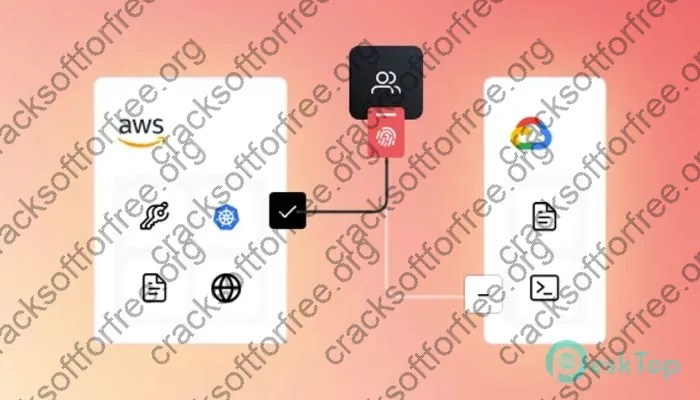
Integrating Boundary Enterprise with Existing Infrastructure
One of Boundary Enterprise’s strengths is its flexibility. Whether you’re all-in on the cloud, sticking with on-premises infrastructure, or somewhere in between, Boundary has you covered.
Cloud Provider Integration
Boundary Enterprise plays nice with all major cloud providers:
- AWS: Seamlessly integrate with EC2, EKS, and more.
- Azure: Connect to VMs, AKS clusters, and other Azure resources.
- Google Cloud: Manage access to GCE instances and GKE clusters.
On-premises Integration
Don’t worry, your data center isn’t left out:
- Integrate with existing directory services like Active Directory.
- Manage access to bare metal servers and VMs.
- Secure connections to legacy systems.
Hybrid Deployment Scenarios
For those straddling both worlds, Boundary Enterprise shines:
- Create unified access policies across cloud and on-prem resources.
- Implement consistent security measures regardless of resource location.
- Simplify access management in complex, multi-environment setups.
Security Features of Hashicorp Boundary Enterprise
Security isn’t just a feature in Boundary Enterprise—it’s woven into its very fabric.
Encryption and Data Protection
- All data at rest is encrypted using AES-256.
- In-transit encryption uses TLS 1.2 or higher.
- Encryption keys are automatically rotated on a configurable schedule.
Role-based Access Control (RBAC)
RBAC in Boundary Enterprise Serial Key is both powerful and flexible:
- Define roles based on job functions or responsibilities.
- Assign permissions at a granular level.
- Easily manage access for large teams or complex organizations.
Audit Logging and Compliance
Staying compliant has never been easier:
- Comprehensive audit logs capture all access attempts and changes.
- Logs are tamper-resistant and cryptographically signed.
- Easy integration with SIEM tools for advanced analysis.
Scalability and Performance
As your organization grows, Boundary Enterprise grows with you:
- Horizontal scaling: Add more Boundary nodes to handle increased load.
- Load balancing: Distribute connections across multiple nodes for optimal performance.
- High availability: Deploy in active-active configurations to eliminate single points of failure.
User Management in Boundary Enterprise
Managing users in Boundary Enterprise is intuitive and powerful:
Creating and Managing User Accounts
- Bulk user import from existing directory services.
- Self-service account creation with admin approval workflows.
- Automated account provisioning and deprovisioning.
Implementing Multi-factor Authentication (MFA)
Boundary Enterprise supports various MFA methods:
- Time-based One-Time Passwords (TOTP)
- Hardware security keys (FIDO2)
- SMS-based codes (though not recommended for high-security environments)
Group Policies and Permissions
Simplify management with group-based policies:
- Create groups based on teams, projects, or access levels.
- Assign permissions to groups instead of individual users.
- Easily adjust access as team members change roles.
Automating Workflows with Boundary Enterprise
Automation is key to managing access at scale. Boundary Enterprise offers robust API and integration capabilities:
- RESTful API: Automate every aspect of Boundary management.
- CI/CD Integration: Incorporate access management into your deployment pipelines.
- Terraform Provider: Manage Boundary resources as code.
Example Terraform code snippet for creating a Boundary project:
resource "boundary_scope" "project" {
name = "My Project"
description = "My first Boundary project"
scope_id = boundary_scope.org.id
auto_create_admin_role = true
auto_create_default_role = true
}
Monitoring and Troubleshooting
Keeping Boundary Enterprise running smoothly is crucial. Here’s how to stay on top of things:
Built-in Monitoring Tools
- Real-time dashboards showing active sessions and resource usage.
- Alerts for suspicious activities or system issues.
- Performance metrics to help identify bottlenecks.
Common Issues and Their Solutions
| Issue | Possible Cause | Solution |
|---|---|---|
| Slow connection times | Network latency | Check network routes, consider deploying closer to resources |
| Authentication failures | Misconfigured policies | Review and test access policies |
| High CPU usage | Too many concurrent sessions | Increase resources or add more Boundary nodes |
Best Practices for Maintaining a Healthy Boundary Enterprise Deployment
- Regularly update to the latest version.
- Implement a robust backup strategy for Boundary data.
- Conduct periodic access reviews to remove unnecessary permissions.
- Use infrastructure-as-code to manage Boundary configurations.
- Integrate with your existing monitoring and alerting systems.
Comparing Hashicorp Boundary Enterprise to Alternatives
While Boundary Enterprise Free download is powerful, it’s essential to understand how it stacks up against alternatives:
| Feature | Boundary Enterprise | Open-source Boundary | Traditional VPN |
|---|---|---|---|
| Identity-based access | ✅ | ✅ | ❌ |
| Dynamic host catalogs | ✅ | Limited | ❌ |
| Enterprise support | ✅ | ❌ | Varies |
| Cost | License-based | Free | Varies |
| Scalability | High | Moderate | Limited |
See also:
Case Studies: Boundary Enterprise in Action
Case Study: Global Financial Services Firm
- Challenge: Managing access for 10,000+ employees across 50 countries.
- Solution: Implemented Boundary Enterprise with integration to existing IAM.
- Result: 99.9% reduction in VPN usage, 85% decrease in access-related tickets.
Future Roadmap for Hashicorp Boundary Enterprise
Hashicorp is continually improving Boundary Enterprise. Some exciting features on the horizon include:
- Enhanced AI-powered anomaly detection
- Native integration with more cloud-native services
- Expanded options for biometric authentication
Getting Started with Boundary Enterprise: Tips and Tricks
Ready to dive in? Here are some tips to get you started:
- Start with a pilot project to gain familiarity.
- Engage stakeholders early to align on access policies.
- Leverage Hashicorp’s extensive documentation and community forums.
- Consider professional services for complex deployments.
- Regularly review and update your access policies.
Conclusion: Is Hashicorp Boundary Enterprise Right for Your Organization?
Hashicorp Boundary Enterprise Crack represents a significant leap forward in access management. Its identity-based approach, coupled with powerful automation and monitoring capabilities, makes it a compelling choice for organizations grappling with the complexities of modern infrastructure.
While it requires an initial investment in both time and resources, the long-term benefits in terms of security, efficiency, and scalability are substantial. As we move further into an era of distributed systems and remote work, tools like Boundary Enterprise will become not just useful, but essential.
Whether you’re a small startup or a large enterprise, if you’re looking to future-proof your access management strategy, Hashicorp Boundary Enterprise deserves a serious look. It’s not just about keeping up with the times—it’s about staying ahead of the curve in an ever-evolving digital landscape.
The speed is a lot enhanced compared to older versions.
The performance is so much enhanced compared to the previous update.
The speed is a lot better compared to older versions.
The recent capabilities in version the latest are really great.
I would highly suggest this tool to professionals wanting a high-quality product.
The application is truly fantastic.
The responsiveness is so much faster compared to last year’s release.
The loading times is significantly enhanced compared to the previous update.
I love the new layout.
The responsiveness is so much better compared to older versions.
It’s now much more user-friendly to finish tasks and track data.
I love the improved UI design.
I would definitely recommend this software to professionals needing a top-tier platform.
The loading times is significantly better compared to the previous update.
It’s now a lot more user-friendly to complete projects and track data.
The application is truly great.
I would definitely endorse this program to professionals needing a top-tier platform.
The speed is a lot enhanced compared to older versions.
The performance is so much enhanced compared to the original.
The latest enhancements in release the newest are incredibly great.
The latest updates in update the newest are really great.
I would strongly recommend this tool to anybody looking for a powerful solution.
The responsiveness is significantly enhanced compared to the original.
The speed is a lot faster compared to the previous update.
It’s now far more user-friendly to complete tasks and organize information.
The loading times is so much enhanced compared to older versions.
The responsiveness is significantly improved compared to older versions.
It’s now far easier to finish work and organize information.
It’s now much easier to finish jobs and track content.
The new capabilities in version the newest are extremely helpful.
The responsiveness is so much faster compared to last year’s release.
This software is truly great.
The latest functionalities in release the latest are so useful.
It’s now a lot easier to get done tasks and organize content.
This tool is really awesome.
The platform is absolutely fantastic.
I absolutely enjoy the enhanced dashboard.
I really like the upgraded layout.
The latest features in version the latest are extremely helpful.
I would absolutely suggest this application to anybody needing a high-quality product.
I would highly endorse this application to anybody looking for a powerful solution.
This application is definitely impressive.